AppTraffic — mobile network forensics, usable by non-engineers
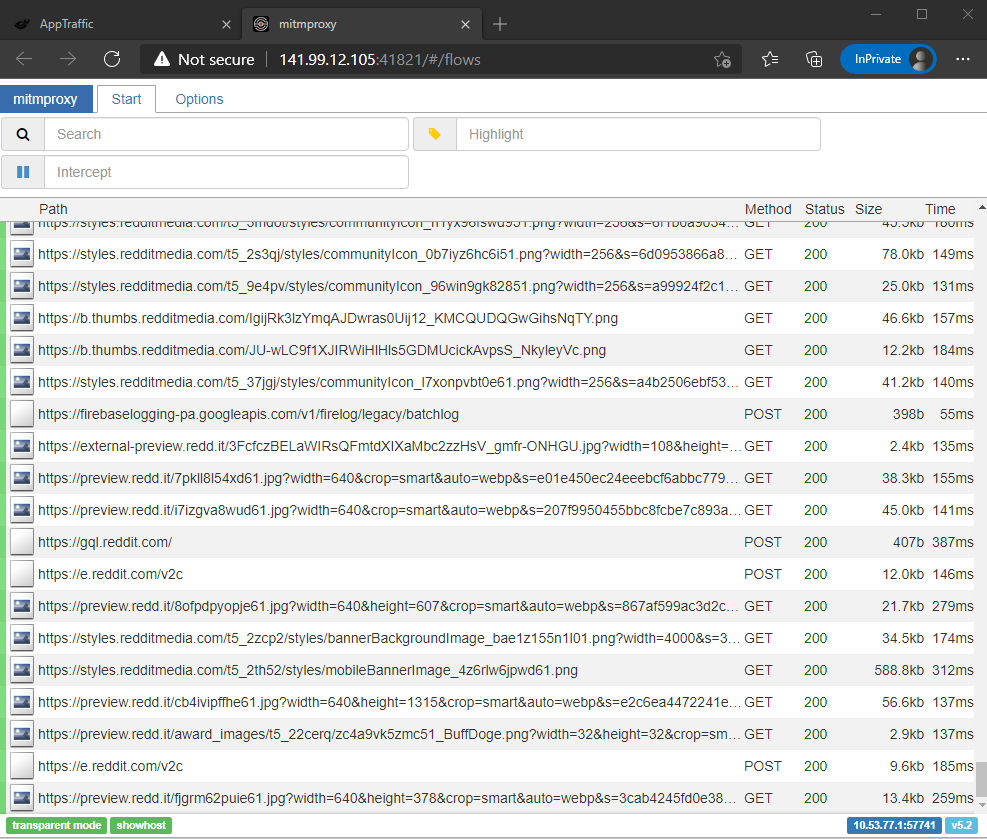
A browser-operated platform that gives privacy and platform-studies researchers live access to the network traffic of any Android or iOS app — without a networking background.
Live at apptraffic.phil.uni-siegen.de — the Siegen-hosted instance. A tool for the other end of the APK analysis pipeline: what’s on the wire, not what’s in the binary.
Between 2020 and 2024, at the SFB 1187 “Media of Cooperation” (University of Siegen), I built AppTraffic. Pick a mobile app in a browser; it runs inside a disposable sandbox device; every network request it makes is captured, TLS-terminated bodies included. No tcpdump, no mitmproxy on the researcher’s laptop, no Wireshark tutorial.
AppTraffic is the sibling of AppInspect. AppInspect: what is in the code. AppTraffic: what happens when it runs.
The problem
Standard mobile-traffic analysis is a seven-step workflow: install an HTTPS interceptor, trust a custom CA on the device, bypass certificate pinning, route traffic through a VPN, capture, decode, search. Every step filters out researchers whose expertise is in what they are looking for, not the tooling.
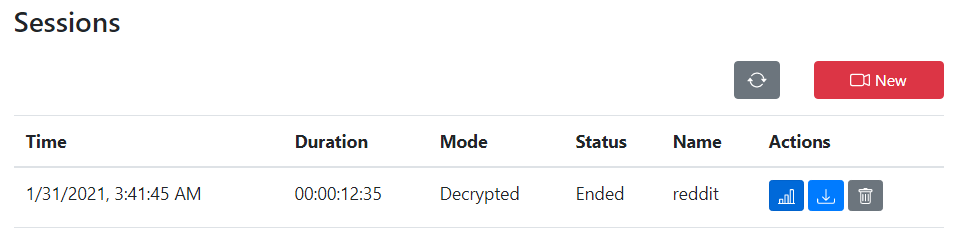
AppTraffic collapses that to: log in, pick an app, press a button, watch requests come in.
Architecture
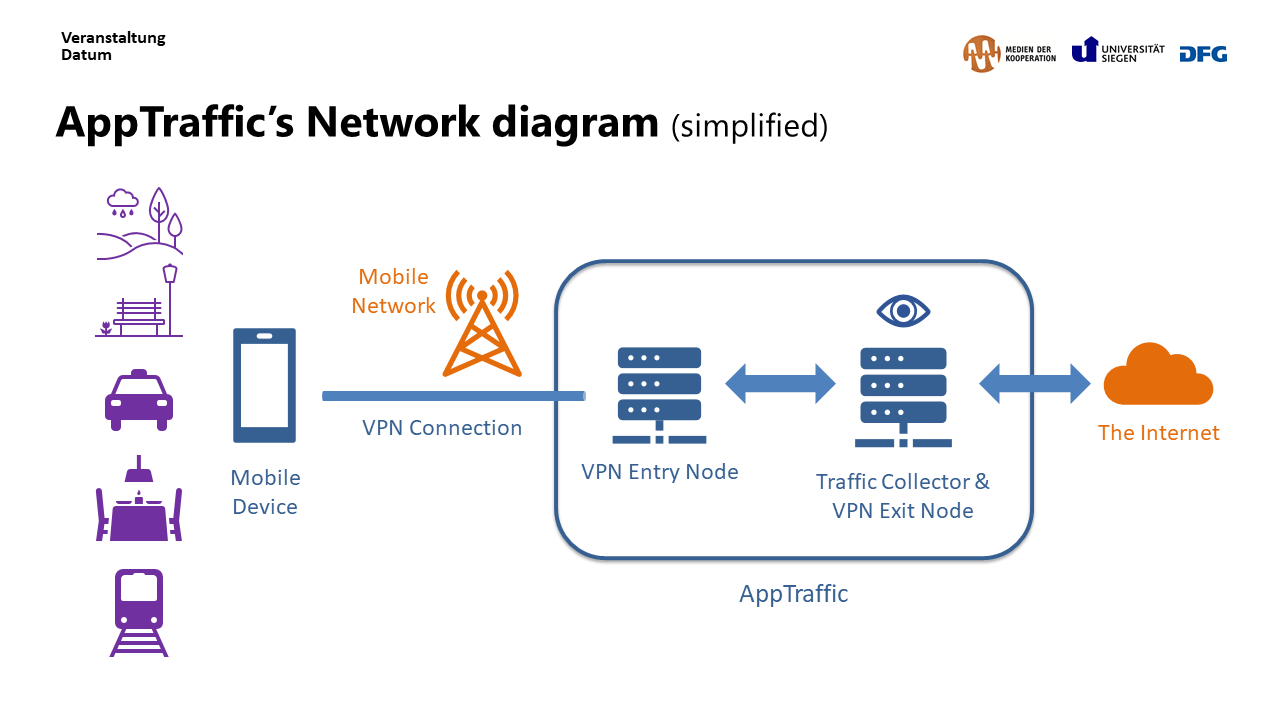
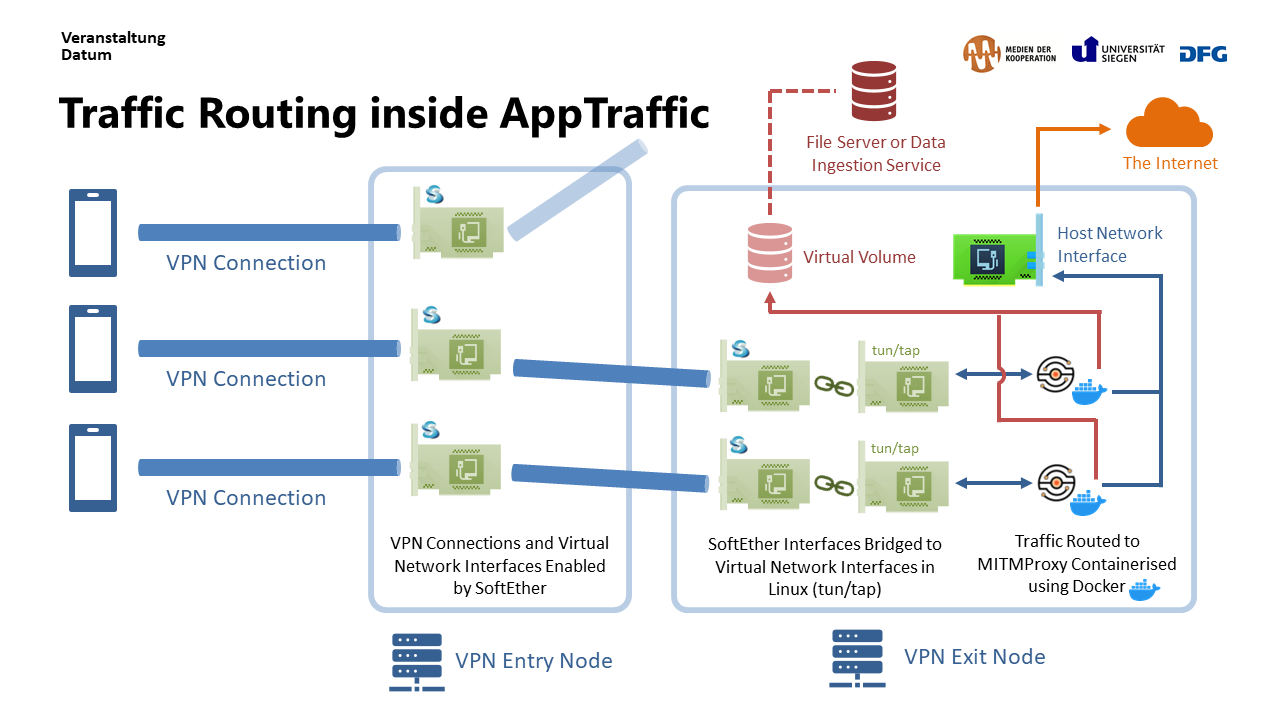
- Sandbox — a pool of Dockerised Android environments (custom root CA, MITMProxy HTTPS interceptor, VPN route). iOS runs on physical devices; simulators cannot route real App Store traffic.
- Session — per-researcher SoftEther VPN terminations keyed to browser identity. Session state in Redis.
- Query — captured flows in MongoDB, filterable by host, endpoint, method, body substring, or time window. Export as JSON, PCAP, or CSV.
Horizontal scaling on the sandbox tier is what keeps costs sane: a Digital Methods Initiative Winter School may mean 40 concurrent sessions on Tuesday and zero on Friday.
The UI, the load-bearing part
Why SoftEther, not WireGuard
A reasonable peer-review question. SoftEther tunnels over HTTPS and works unmodified from networks that filter UDP. Researchers on institutional Wi-Fi regularly hit those filters. WireGuard is cleaner to operate; SoftEther is harder to block.
Impact
- Used by researchers from 8+ European universities — many from non-technical disciplines (media studies, platform studies, digital sociology). Adoption grew through the Digital Methods Initiative teaching programme (Winter / Summer Schools), not procurement: the tool demands no networking or systems-engineering background, which was the explicit design goal.
- Presented at RSECon 2023.
- Underpinned the empirical work of several papers.
Publications
Methodology and digital-methods application of AppTraffic appear in:
Chao, J., van Geenen, D., Gerlitz, C. & van der Vlist, F. N. (2024). Digital methods for sensory media research: Toolmaking as a critical technical practice. Convergence: The International Journal of Research into New Media Technologies, 30(1), 236–263. https://doi.org/10.1177/13548565241226791
Pilipets, E. & Chao, J. (2025). Noise in sonic social media: Memetic soundscapes of Deep TikTok. New Media & Society. https://doi.org/10.1177/14614448251358752
Omena, J. J., Lobo, T., Tucci, G., Bitencourt, E., de Keulenaar, E., Kerche, F. W., Chao, J., Liedtke, M., Li, M., Paschoal, M. L. & Lavrov, I. (2024). Quali-quanti visual methods and political bots: A cross-platform study of pro- & anti-bolsobots. Journal of Digital Social Research, 6(1), 50–73. https://doi.org/10.33621/jdsr.v6i1.215
AppTraffic was built at the SFB 1187 “Media of Cooperation”, University of Siegen.